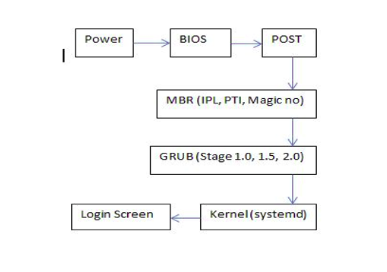
Here is a quick overview of the Linux Boot Process, if you are a little rusty. After all, it’s not every day that you need to look into, troubleshoot or adjust the boot process of a Linux box. This might come handy before your next SysAdmin job interview too.
Category: Linux
Linux is my primary operating system. I used it on the servers, desktops, laptops, netbooks, and even mobile phones since approximately 1997. I’ve tried a number of distributions over the years, and even created a couple myself. I still look around sometimes to see what others are up to. But most of my machines are running some sort of Red Hat – either a quick and easy Fedora Linux, or a stable and secure Red Hat Enterprise Server, or a cheaper CentOS alternative.
And while by now I am very comfortable in the Linux environment (both graphical and command line), I still discover a lot of new and interesting things about it. When I come across something worthy, I usually share it with the rest of the Open Software world, using this category.
Lumina Desktop 1.0.0 released
Linux Weekly News shares the announcement from the Lumina Desktop project about the release of the version 1.0.0.
And while I’m still pretty happy with my MATE desktop, it’s nice to see people taking an effort into making things better. Two particular features caught my eye in the release announcement:
Multiple-monitor support! Each monitor is treated as an independent entity – making it great for presentation systems which use a temporary monitor or for workstations which utilize an array of monitors for various tasks.
This is super cool! Current iterations of Gnome and KDE do support multi-monitor setups, but they treat all monitors as a single work space. Using multiple virtual work spaces is supported, but one can’t switch a work space on a particular monitor without switching the corresponding work space on all other monitors. I haven’t tried Lumina Desktop myself yet, but from the announcement it looks like they support exactly that – switching monitor work spaces individually and not all together.
Personalize the initial settings for users with a single configuration file!
This is how things used to be in the old days (back when I was using AfterStep and the like). A single configuration file is super convenient when you want to move your setup from machine to machine. Both Gnome and KDE these days utilize numerous configuration files and GUI tools to manage them, which makes automating these setups with tools like Ansible very impractical.
I’m way too busy with work stuff these days to try a different desktop environment, but I will keep an eye on the Lumina Desktop Environment for now. Maybe one slow Friday I’ll give it a spin.
Setting up NAT on Amazon AWS
When it comes to Amazon AWS, there are a few options for configuring Network Address Translation (NAT). Here is a brief overview.
NAT Gateway
NAT Gateway is a configuration very similar to Internet Gateway. My understanding is that the only major difference between the NAT Gateway and the Internet Gateway is that you have the control over the external public IP address of the NAT Gateway. That’ll be one of your allocated Elastic IPs (EIPs). This option is the simplest out of the three that I considered. If you need plain and simple NAT – than that’s a good one to go for.
NAT Instance
NAT Instance is a special purpose EC2 instance, which is configured to do NAT out of the box. If you need anything on top of plain NAT (like load balancing, or detailed traffic monitoring, or firewalls), but don’t have enough confidence in your network and system administration skills, this is a good option to choose.
Custom Setup
If you are the Do It Yourself guy, this option is for you. But it can get tricky. Here are a few things that I went through, learnt and suffered through, so that you don’t have to (or future me, for that matter).
Let’s start from the beginning. You’ve created your own Virtual Private Cloud (VPC). In that cloud, you’ve created two subnets – Public and Private (I’ll use this for example, and will come back to what happens with more). Both of these subnets use the same routing table with the Internet Gateway. Now you’ve launched an EC2 instance into your Public subnet and assigned it a private IP address. This will be your NAT instance. You’ve also launched another instance into the Private subnet, which will be your test client. So far so good.
This instance will be used for translating internal IP addresses from the Private subnet to the external public IP address. So, we, obviously, need an external IP address. Let’s allocate an Elastic IP and associate it with the EC2 instance. Easy peasy.
Now, we’ll need to create another routing table, using our NAT instance as the default gateway. Once created, this routing table should be associated with our Private subnet. This will cause all the machines on that network to use the NAT instance for any external communications.
Let’s do a quick side track here – security. There are three levels that you should keep in mind here:
- Network ACLs. These are Amazon AWS access control lists, which control the traffic allowed in and out of the networks (such as our Public and Private subnets). If the Network ACL prevents certain traffic, you won’t be able to reach the host, irrelevant of the host security configuration. So, for the sake of the example, let’s allow all traffic in and out of both the Public and Private networks. You can adjust it once your NAT is working.
- Security Groups. These are Amazon AWS permissions which control what type of traffic is allowed in or out of the network interface. This is slightly confusing for hosts with the single interface, but super useful for machines with multiple network interfaces, especially if those interfaces are transferred between instances. Create a single Security Group (for now, you can adjust this later), which will allow any traffic in from your VPC range of IPs, and any outgoing traffic. Assign this Security Group to both EC2 instances.
- Host firewall. Chances are, you are using a modern Linux distribution for your NAT host. This means that there is probably an iptables service running with some default configuration, which might prevent certain access. I’m not going to suggest to disable it, especially on the machine facing the public Internet. But just keep it in mind, and at the very least allow the ICMP protocol, if not from everywhere, then at least from your VPC IP range.
Now, on to the actual NAT. It is technically possible to setup and use NAT on the machine with the single network interface, but you’d probably be frowned upon by other system and network administrators. Furthermore, it doesn’t seem to be possible on the Amazon AWS infrastructure. I’m not 100% sure about that, but I’ve spent more time than I had to figure this out and I failed miserably.
The rest of the steps would greatly benefit from a bunch of screenshots and step-by-step click through guides, which I am too lazy to do. You can use this manual, as a base, even though it covers a slightly different, more advanced setup. Also, you might want to have a look at CentOS 7 instructions for NAT configuration, and the discussion on the differences between SNAT and MASQUERADE.
We’ll need a second network interface. You can create a new Network Interface with the IP in your Private subnet and attach it to the NAT instance. Here comes a word of caution: there is a limit on how many network interfaces can be attached to EC2 instance. This limit is based on the type of the instance. So, if you want to use a t2.nano or t2.micro instance, for example, you’d be limited to only two interfaces. That’s why I’ve used the example with two networks – to have a third interface added, you’d need a much bigger instance, like t2.medium. (Which is a total overkill for my purposes.)
Now that you’ve attached the second interface to your EC2 instance, we have a few things to do. First, you need to disable “Source/Destination Check” on the second network interface. You can do it in your AWS Console, or maybe even through the API (I haven’t gone that deep yet).
It is time to adjust the configuration of our EC2 instance. I’ll assume CentOS 7 Linux distribution, but it’d be very easy to adjust to whatever other Linux you are running.
Firstly, we need to configure the second network interface. The easiest way to do this is to copy /etc/sysconfig/network-scripts/ifcfg-eth0 file into /etc/sysconfig/network-scripts/ifcfg-eth1, and then edit the eth1 one file changing the DEVICE variable to “eth1“. Before you restart your network service, also edit /etc/sysconfig/network file and add the following: GATEWAYDEV=eth0 . This will tell the operating system to use the first network interface (eth0) as the gateway device. Otherwise, it’ll be sending things into the Private network and things won’t work as you expect them. Now, restart the network service and make sure that both network interfaces are there, with correct IPs and that your routes are fine.
Secondly, we need to tweak the kernel for the NAT job (sounds funny, doesn’t it?). Edit your /etc/sysctl.conf file and make sure it has the following lines in it:
# Enable IP forwarding net.ipv4.ip_forward=1 # Disable ICMP redirects net.ipv4.conf.all.accept_redirects=0 net.ipv4.conf.all.send_redirects=0 net.ipv4.conf.eth0.accept_redirects=0 net.ipv4.conf.eth0.send_redirects=0 net.ipv4.conf.eth1.accept_redirects=0 net.ipv4.conf.eth1.send_redirects=0
Apply the changes with sysctl -p.
Thirdly, and lastly, configure iptables to perform the network address translation. Edit /etc/sysconfig/iptables and make sure you have the following:
*nat :PREROUTING ACCEPT [48509:2829006] :INPUT ACCEPT [33058:1879130] :OUTPUT ACCEPT [57243:3567265] :POSTROUTING ACCEPT [55162:3389500] -A POSTROUTING -s 10.0.0.0/16 -o eth0 -j MASQUERADE COMMIT
Adjust the IP range from 10.0.0.0/16 to your VPC range or the network that you want to NAT. Restart the iptables service and check that everything is hunky-dory:
- The NAT instance can ping a host on the Internet (like 8.8.8.8).
- The NAT instance can ping a host on the Private network.
- The host on the Private network can ping the NAT instance.
- The host on the Private network can ping a host on the Internet (like 8.8.8.8).
If all that works fine, don’t forget to adjust your Network ACLs, Security Groups, and iptables to whatever level of paranoia appropriate for your environment. If something is still not working, check all of the above again, especially for security layers, IP addresses (I spent a coupe of hours trying to find the problem, when it was the IP address typo – 10.0.0/16 – not the most obvious of things), network masks, etc.
Hope this helps.
504 Gateway Timeout error on Nginx + FastCGI (php-fpm)
“504 Gateway Timeout” error is a very common issue when using Nginx with PHP-FPM. Usually, that means that it took PHP-FPM longer to generate the response, than Nginx was willing to wait for. A few possible reasons for this are:
- Nginx timeout configuration uses very small values (expecting the responses to be unrealistically fast).
- The web server is overloaded and takes longer than it should to process requests.
- The PHP application is slow (maybe due to database behind it being or slow).
There is plenty advice online on how to troubleshoot and sort these issues. But when it comes down to increasing the timeouts, I found such advice to be scattered, incomplete, and often outdated. This page, however, has a good collection of tweaks. They are:
- Increase PHP maximum execution time in /etc/php.ini: max_execution_time = 300
- Increase PHP-FPM request terminate timeout in the pool configuration (/etc/php-fpm.d/www.conf): request_terminate_timeout = 300
- Increase Nginx FastCGI read timeout (in /etc/nginx/nginx.conf): fastcgi_read_timeout 300;
Also, see this Stack Overflow thread for more suggestions.
P.S.: while you are sorting out your HTTP errors, have a quick look at HTTP Status Dogs, which I blogged about a while back.
Kali Tools – Linux distribution for penetration testing
Kali Tools – a special purpose Linux distribution for performing penetration testing. A long list of tools is split into the following categories:
- Information gathering
- Vulnerability analysis
- Wireless attacks
- Web applications
- Exploitation tools
- Forensic tools
- Stress testing
- Sniffing & spoofing
- Password attacks
- Maintaining access
- Reverse engineering
- Hardware hacking
- Reporting tools