Whether you are an experienced shell user, or just a newbie, have a look at this article for a collection of the great tools and examples of how to process text in the shell. It includes all the usual suspects: cat, head, tail, wc, grep, cut, paste, sort, uniq, awk, tr, fold, and sed. Great examples and real life scenarios for each are also provided, with the logic explained and more complex use cases broken down into steps.
Category: Sysadmin
System administration is a special are of IT. It also has a special place in my heart. It is an interesting mixture of all the other disciplines, both common across the whole industry, and at the same time unique for each person, company, and geographical location. When I have something to say or share about system administration, I use this category.
ctop – top-like interface for monitoring Docker containers
ctop is a very simple, but very useful tool for when you run a number of Docker containers and want to have a top-like overview of their CPU, memory, and network usage.
This article provides more details on how to install, run, and use ctop effectively, including container filtering, single container view, etc.
k6 – API performance testing tool
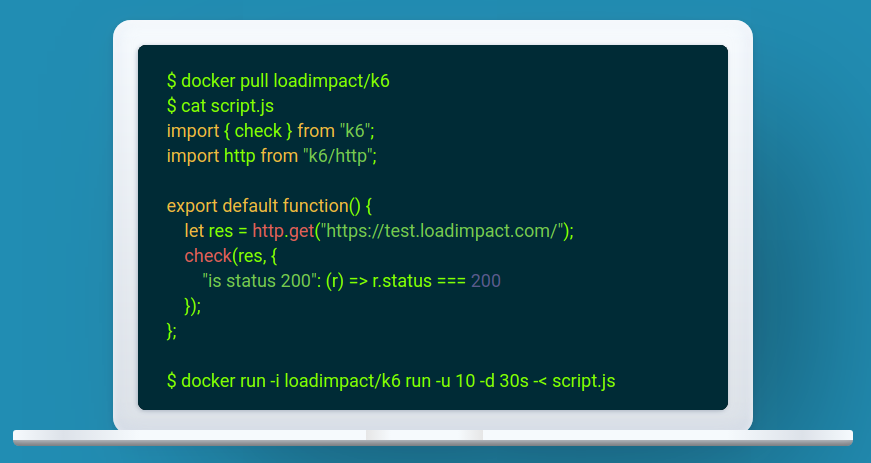
k6 is a developer centric open source load and performance regression testing tool for testing the performance of your cloud native backend infrastructure: APIs, microservices, serverless, containers and websites. It’s built to integrate well into your development workflow and CI/CD automation pipelines.
This is one of the better tools that I’ve seen in a long time. Not only it does its job great, but it integrates brilliantly with your development and testing pipelines.
You can either build your tests from scratch, or you can convert import them from your existing tools. For example, Postman collections, environments, and tests can be converted to k6 with postman-to-k6. Here’s a blog post to get you started on that path.
Side note: if you hit the “EACCES: permission denied, mkdir ‘/usr/local/lib/node_modules/postman-to-k6/vendor’” durin the postman-to-k6 installation, then simply append “–unsafe-perm=true –allow-root” to the “npm install” command, as suggested in this GitHub thread.
k6 provides excellent functionality for extending your basic performance tests with additional checks, metrics, and thresholds. You can even keep using your existing Postman tests within k6.
There’s also a variety of output formats, ranging from CSV and JSON, all the way to InfluxDB with Grafana charts.
dive – Docker image explorer
dive is a Docker image explorer. This is a very handy tool when you are trying to figure out how a Docker image was built and what’s in it, and you don’t have the original Dockerfile.
It uses the meta information for each layer to show you which command was used to create the layer, and which files were added, removed, or changed.
Additionally, you can use dive to make sure your Docker images are optimized and their size is under control. You can even integrate dive into your CI/CD pipeline!
Fedora 31: Docker Fix
I’ve updated my laptop to Fedora 31 over the Christmas holidays. Pretty much everything works as it did before. Except for Docker, which suddenly fails to start the service.
A quick Google search pointed to the discussion in this bug report, where I found the solution that worked for me:
- Edit /etc/sysconfig/grub
- Append systemd.unified_cgroup_hierarchy=0 to the GRUB_CMDLINE_LINUX variable
- Run “grub2-mkconfig -o /boot/efi/EFI/fedora/grub.cfg“
- Reboot
Once the machine came back up, docker service was running normally.